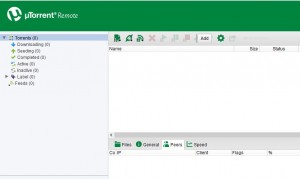
 We sat, had a few drinks, he told me he had a couple of Open Source Projects he was working on and also described the technologies he had implemented to get one of his projects going. “Wait! Do these things actually exist?!” I asked… “Yes they do!”, he replied. Okay, I think I am going a little bit fast here; It all started when I was having a chat with one of my associates (long time close associate to be exact), he was telling me how excited he was to have spent the last couple of months investing in learning and implementing Open Source based Server Solutions. Most of his projects initially started / start off by him downloading a couple of Linux based software(s) (.iso images) in the form of torrents from Distrowatch using his TorrentBox. “What did you say, TorrentBox?” I asked, “Wait! Do these things actually exist?!” I asked (again (without even giving him the chance to answer))… “Yes they do!”, he replied. My questions or reasoning didn’t seem to move him, neither did his projects (as a whole)! His major concern was
We sat, had a few drinks, he told me he had a couple of Open Source Projects he was working on and also described the technologies he had implemented to get one of his projects going. “Wait! Do these things actually exist?!” I asked… “Yes they do!”, he replied. Okay, I think I am going a little bit fast here; It all started when I was having a chat with one of my associates (long time close associate to be exact), he was telling me how excited he was to have spent the last couple of months investing in learning and implementing Open Source based Server Solutions. Most of his projects initially started / start off by him downloading a couple of Linux based software(s) (.iso images) in the form of torrents from Distrowatch using his TorrentBox. “What did you say, TorrentBox?” I asked, “Wait! Do these things actually exist?!” I asked (again (without even giving him the chance to answer))… “Yes they do!”, he replied. My questions or reasoning didn’t seem to move him, neither did his projects (as a whole)! His major concern was
 Trevor Murimba
Trevor Murimba
2016 Trend Micro Security Predictions: The Fine Line
![]() 2016 Trend Micro Security Predictions: The Fine Line
2016 Trend Micro Security Predictions: The Fine Line
Author: Trend Micro Security Team
Source: http://www.trendmicro.com/
Overview: Every year, the triumphs and failures reflected in cyber security stories not only leave us with valuable lessons but also hints of the foreseeable future. Looking closely, we get to pick pieces of the puzzle that we can use to build a vivid picture of what’s to come. Read More
Security by Obscurity, really?
 Oh YES, Oh YES, really! Wait!, what!, NO! NO I mean YES! but…? Well, it all started when me and one of my ‘Skiddy’ friends went for a sleep over at our ‘Geeky’ friends place. The first few words that came out of his mouth (Skiddy friend) as we walked into our (Geeky friend’s) flat was, “I wish you had WiFi so I could connect to it and show you this web-based (bandwidth intense) app I have running remotely on one of my Servers but then again, I am picking up other WiFi signals, unfortunately their signals are really weak, like my Hacking skills!” (laughing) He went on to say, “If only I had mad skills (l337 h4x0r), I would have connected to one of the nearby WiFi’s, piggybacked it’s Internet connection to show you!” My Geeky friend replied, “I do have WiFi but it’s because of people like you it’s running in stealth mode!” It immediately registered and he (Skiddy friend) replied,
Oh YES, Oh YES, really! Wait!, what!, NO! NO I mean YES! but…? Well, it all started when me and one of my ‘Skiddy’ friends went for a sleep over at our ‘Geeky’ friends place. The first few words that came out of his mouth (Skiddy friend) as we walked into our (Geeky friend’s) flat was, “I wish you had WiFi so I could connect to it and show you this web-based (bandwidth intense) app I have running remotely on one of my Servers but then again, I am picking up other WiFi signals, unfortunately their signals are really weak, like my Hacking skills!” (laughing) He went on to say, “If only I had mad skills (l337 h4x0r), I would have connected to one of the nearby WiFi’s, piggybacked it’s Internet connection to show you!” My Geeky friend replied, “I do have WiFi but it’s because of people like you it’s running in stealth mode!” It immediately registered and he (Skiddy friend) replied,
